A5/1 is in the Air: Passive Detection of 2G (GSM) Ciphering Algorithms
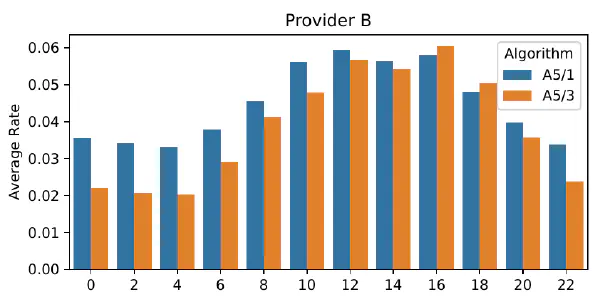
This paper investigates the ongoing use of the A5/1 ciphering algorithm within 2G GSM networks. Despite its known vulnerabilities and the gradual phasing out of GSM technology by some operators, GSM security remains relevant due to potential downgrade attacks from 4G/5G networks and its use in IoT applications. We present a comprehensive overview of a historical weakness associated with the A5 family of cryptographic algorithms. Building on this, our main contribution is the design of a measurement approach using low-cost, off-the-shelf hardware to passively monitor Cipher Mode Command messages transmitted by base transceiver stations (BTS). We collected over 500,000 samples at 10 different locations, focusing on the three largest mobile network operators in Germany. Our findings reveal significant variations in algorithm usage among these providers. One operator favors A5/3, while another surprisingly retains a high reliance on the compromised A5/1. The third provider shows a marked preference for A5/3 and A5/4, indicating a shift towards more secure ciphering algorithms in GSM networks.